zveloLABS™ has been tracking compromised sites that host PageRank Bombs since 2008. The attacker hacks a site, but instead of putting exploits on the hacked site, they put links to other websites in order to boost the search result ranking on various search engines. Initially this was being used for ad sites, porn sites, and pharma fraud sites. Now, however, it is being used to boost the results of malicious sites, but with a new twist that targets Google users.
The sites whose search engine ranking is being boosted are now serving up malware through a complex series of redirects. However, the redirects and the malware are only served up if the user gets to the site after clicking the link on Google. Going directly to the malicious site (by pasting into your browser directly) results in a harmless page.
For example, using Google, a search for “nhl all-time scoring leaders” returns several malicious results on the first page (in the 5th, 6th, 7th, 8th and 10th positions).
Going to the website, hxxp://adoptabeach.org/zzbtw/colzw/leaders.php, directly results in an innocuous page.
[Note: Extreme caution should still be taken before visiting any websites listed in this post.]
However, clicking the link in the Google search results will bring the user to a web site using a common Rogue Anti-Virus template that alerts the user that their PC is infected and prompts unsuspecting users to download what is really a Trojan:
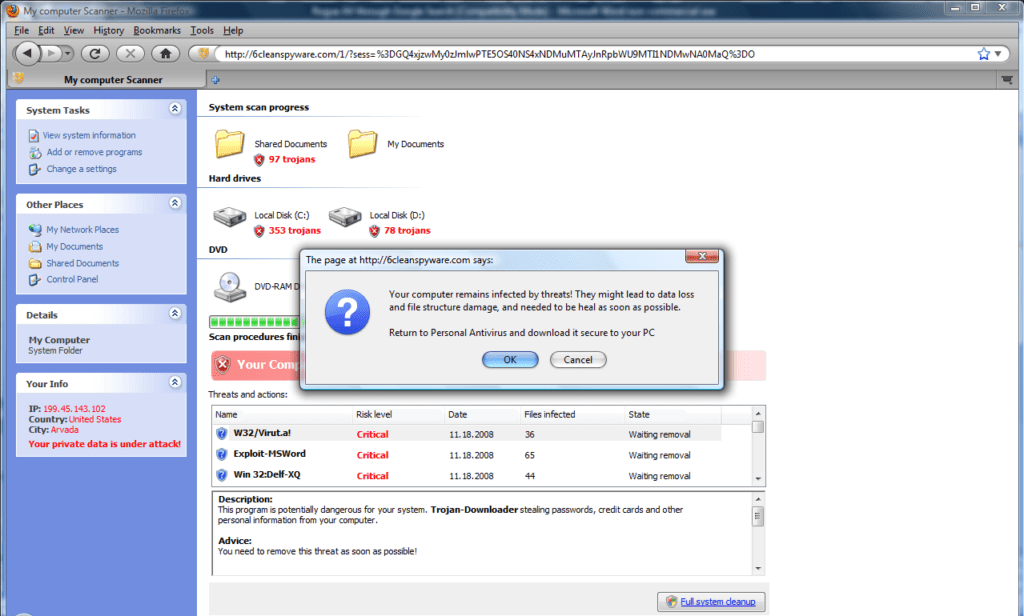
The Trojan being downloaded at this point has only a 7% detection rate by anti-virus software with Microsoft, NOD32 and Panda detecting.
Some of the sites being used include:
hxxp://shanthkherath.com
hxxp://adoptabeach.org
hxxp://advertising-made-easy.com
These redirect through some URLs including:
hxxp://skystats1.net/in.cgi?9
hxxp://skystats1.net/redirect2/
http://jeremy-kyle-now.cn/go.php?id=2004&key=ff0057594&p=1
As far as zveloLABS™, the referrer must have this string, google.com/search?q=, in it and the User-Agent must indicate a Windows machine or the malware will not be delivered. It does not appear that users of other search engines or operating systems are yet being targeted.





