Email Spam is dead! Long live Email Spam!
It seems very strange that in the year 2017 (approximately 20 years from when the commercial use of the Internet first became possible), we are still dealing with email spam with no end in sight. There are many solutions now available in the industry that can be placed in various locations in the network stream that can stop or quarantine email spam before it hits our inboxes. Yet, spam has increased year after year and it is becoming more difficult to stop it or succumb to clicking on malicious bait even by accident.
Spam is an epidemic. It is estimated by various sites from Lifewire, Wikipedia, to Time.com, that about 60% – 80% of all email sent today is spam. To put that into perspective, according to DMR’s Email report located here, as of January 2017, approximately 270 billion (with a B), emails were sent daily. How does the math look? It’s okay you don’t have to do the math because I went ahead and did this for you. If these numbers are close to reality, it would mean that approximately 160 – 216 billion spam emails per day.
As we have seen over the decades, email spam has morphed and changed from unsolicited email from various companies asking you to take a look at their products and/or services. You never asked to be sent these “junk” email but the spammer(s) sent them anyway. However what was first a nuisance of just junk email, it has turned into a way to scam people out of money or in today’s cases grabbing important personal data to create malicious activity at a larger scale.
Email spam (or email scam) used to be about asking users to claim inheritance money from Nigerian princes, or virtual/fake pharmacies offering low prices on medication but now they are more creative. These spammers create elaborate sites for phishing, spread ransomware or malware for other malicious or criminal activities.
711 million email addresses ensnared
A Paris-based security researcher Benkow moʞuƎq discovered an open and accessible web server hosted in the Netherlands. This server stores (or stored since law enforcement has been contacted and may have taken down the site) dozens of text files containing a huge batch of email addresses, passwords, and email servers used to send spam.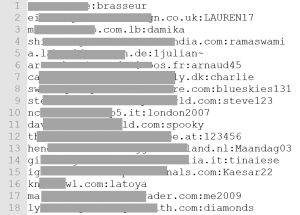
Troy Hunt, who is an analyst, blogger and runs breach notification site “Have I been Pwned”, gives a great play by play about the data on this massive list. I have included an image from Troy’s site to show an example of the data that was in one of the files on this site. ZDNet’s story by Zack Whittaker, provides a great overview of the event as well.
To summarize their stories, approximately 711 Million email addresses were being stored and used by a large scale spambot/malware operation. This large amount of information was used to bypass spam filters by sending email through legitimate email servers.
Back in the day, spammers had to rely on “open” relay email servers that didn’t require authentication but that type of openness is now all but closed and thus spammers and malware operations had to use other means. With legitimate email addresses and current working passwords, this malicious operation could now send anything through email without being stopped by spam blockers or other spam/phishing blocking tools. Not only that, but with legitimate email addresses being used; friends and family of this legitimate user would be fooled into thinking that emails from this person are legitimate and thus would not think twice about clicking on or opening an attachment. Or if the targets would receive this email from these legitimate users, attachments or links could be inquiring about invoices, past due bills, delivery services, hotel reservations…the list goes on and on.
So the days of the Nigerian virtual pharmacy sex pills spam emails have shifted dramatically to the point of not knowing what email from whom to trust anymore.
What zvelo has seen after investigating this large spambot operation that some of these files, email templates and/or attachments contained malicious or suspicious URLs. Approximately 75% of the URLs we obtained were marked correctly in our zveloDB as malicious before the story broke. The other URLs that were not categorized as such were new to zvelo, no longer responding or the web server owners have already taken down the malicious content and is no longer present. This type of malicious operation is another example of why zvelo has built its product and services to address the dynamically changing internet. We have invested heavily on our infrastructure, products, and processes to revisit sites often, quickly address the churn of site content, and lastly dealing with these fly by night malicious websites in a proactive manner.





