The Strategic, Operational, and Tactical Levels of Cyber Threat Intelligence
Over the past several months, zvelo has introduced our take on Cyber Threat Intelligence (CTI). Specifically, we have presented the CTI Process Feedback Loop in its entirety, in addition to delivering reports on Malicious Trends and the Emotet malware family. This blog aims to define the strategic, operational, and tactical levels of Cyber Threat Intelligence, provide a description of who uses CTI in organizations — big and small — including example uses cases, and last, how zveloCTI can help meet those needs. It is important to note that CTI is not the answer to every question. CTI should be part of a holistic cyber defense approach which supports the entire defense-in-depth — including data, applications, endpoints, network, perimeter, and now home offices.
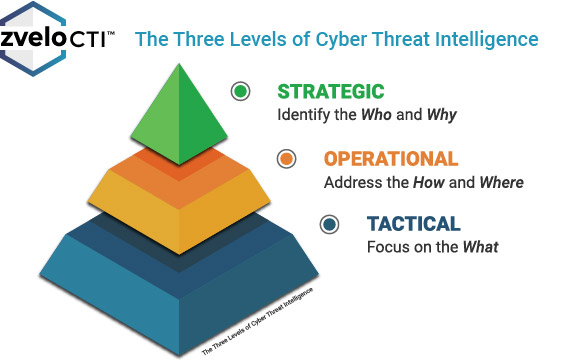
Cyber Threat Intelligence is typically viewed in three levels:
- Strategic: Identifies the Who and Why
- Operational: Addresses the How and Where
- Tactical: Focuses on the What
Strategic Cyber Threat Intelligence
CTI at the strategic level identifies the who and why to provide organizations with crucial insight. It aims to identify who is behind a specific threat/family of threats, while addressing ongoing trends. CTI at the strategic level is also about the why. Why is an organization an organization being targeted? Why is a specific malicious cyber actor (MCA) or group of MCAs interested in an organization or industry vertical — for example, healthcare? In many cases, strategic level CTI can be tied to Advanced Persistent Threats (APT) activities although not always.
Operational Cyber Threat Intelligence
CTI at the operational level addresses the how and where. The observed threat actor Tactics, Techniques, and Procedures (TTP) define the how of CTI. The how goes beyond just an alert, or series of alerts. The how assists organizations to understand the extent of a breach, or prepare defense in advance. The where of CTI helps organizations conduct threat hunts proactively, in advance of a compromise, or after an incident when recovery has begun. In general terms, you cannot catch the MCAs in an environment unless you know where to look.
Tactical Cyber Threat Intelligence
CTI at the tactical level focuses on the what. Indicators of Compromise (IOC) such as file names, file hashes, domain names, IP addresses, and much more, define the what of CTI. IOCs can be used to triage and validate alerts, support rules for firewalls or intrusion detection/prevention systems, endpoint detection & response systems, and other similar capabilities. The what takes the form of internally generated data which resides in Security Operations Centers (SOC) and, more often than not, is organized into multiple trusted feeds that are hopefully tuned to the organization’s environment.
Now that we’ve defined what each of the different levels cover, let’s move on and cover the types of users, why, and how each of the cyber threat intelligence levels can be used based on some of the most common use case scenarios that cyber defenders encounter.
Who Uses Strategic CTI, Why, and How?
In most organizations, strategic CTI users are individuals in the “C-Suite” — the Chief Executive Officer, Chief Financial Officer, Chief Information Officer, and so on depending on structure. In other words, these personnel are the high-level executives, leaders, and management of an organization. Strategic users consume cyber threat intelligence data to gain an understanding of top-level trends and threats to the organization. They may or may not have a technical background, and they utilize CTI to support their needs when making risk-based decisions regarding staffing, technologies, cybersecurity requirements, and ultimately budgets. Without the threat intelligence information, strategic users may lack information critical to procuring the necessary resources to secure their organization.
Strategic Cyber Threat Intelligence Use Case: Brand Exposure Intelligence
One prevalent use case for strategic CTI users is brand exposure intelligence. There are multiple data points to consider here including cybersquatting (also known as domain or subdomain squatting), domain or subdomain hijacking, phishing campaigns, and exploited web-pages/parts. Assessing exposures in each of these areas helps strategic users understand how their brand is being co-opted by MCAs to exploit their customers. Have MCAs taken over existing or forgotten exposed internet infrastructure? Should they purchase additional domains to thwart MCAs? Using CTI to explore and understand brand exposure is an easy way for strategic users to protect both their organizations and customers which improves the bottom line.
Who Uses Operational CTI, Why and How?
Operational CTI users in an organization include a wide variety of personnel including, but not limited to: Incident responders and teams, network defenders, host analysts, malware analysts, forensic analysts, and more. Large institutions commonly employ all of these work roles, while smaller organizations tend to have fewer capabilities and may, or may not, contract for them. Operational users consume CTI for technical context, with a focus on the IOCs themselves, related linkages, and whether or not they might be found in the environments they are responsible for securing. Context is critical for operational users because every environment is unique in how they use various technology stacks. For example, if your environment uses all Windows and no Linux, you should not blindly ingest every new Intrusion Detection System (IDS) rule that gets released. There is no value in spending IDS processing cycles on rules that don’t apply to your environment.
Operational Cyber Threat Intelligence Use Case: Threat Hunting
For operational users, a frequent CTI use case is for Threat Hunting. Threat Hunting pulls from multiple sources, including CTI, to leverage all available IOCs that are applicable to an environment and proactively look for evidence of MCA activities. Threat Hunting starts with a hypothesis, usually based on the hunter’s intuition or one or two pieces of data that, on the surface, appear unrelated. The hunter — a host analyst or network defender — then leverages CTI to expand on the pieces of information related to the hypothesis, and either confirms it or moves on to the next concern. Without tailored and trusted CTI, it is nearly impossible to conduct Threat Hunting successfully.
Who Uses Tactical CTI, Why and How?
Every organization has tactical users who need CTI. From the largest organizations with dedicated SOCs, to the smallest who only have a few cyber defenders or may have outsourced to an Managed Security Service Providers (MSSP), reliable CTI is essential in today’s ever increasing threat landscape. Tactical users are on the frontlines of an organization’s cyber defenses. They manage everything from firewalls, IDS/IPS systems, security gateways, Security Information & Event Monitoring (SIEM) systems, Security Orchestration, Automation and Response (SOAR) capabilities, Endpoint Detection and Response (EDR), and so on. Tactical users leverage CTI provided IOCs, content, and context to directly prevent MCA attacks on their organizations. Since the MCA ‘haystack’ is so large, and the ‘needles’ so well hidden, tactical users need CTI reliable sources that do not generate a large number of false positives. There simply is not enough time to chase down useless or irrelevant leads.
Tactical Cyber Threat Intelligence Use Case: Triage
The most straightforward CTI use case for tactical users is triage. Regardless of whether the tactical user is in an SOC, MSSP, or an organization with only a couple of cyber defenders, CTI can help quickly identify whether or not there is cause for concern. In a triage case, tactical users first check their local CTI store, or call the APIs of their CTI sources. If there is an IOC match, they move forward with their incident handling process. If there is no match, they move onto the next alert. Utilizing CTI in a “verify, then trust” construct can significantly reduce the amount of time analysts at the tactical level must spend to differentiate between good and bad.
Who Are the Other CTI Users?
Organizing all those who use cyber threat intelligence into bins of Strategic, Operational, and Tactical helps codify CTI consumption from a cyber-focused perspective. However, it is important to consider the broader use of cyber threat intelligence across today’s technology enabled organizations. First, consider the business units, or departments, of an organization. Do legal, auditing, risk management, and other functional units need CTI support? Absolutely! The level of support will depend on the organization’s mission, requirements, and exposures. Every organization will be different and there will not be a cookie cutter solution.
Let’s not forget about internal stakeholders. Stakeholders are those members of an organization who can directly influence resources when it comes to cybersecurity. Stakeholders can be end users, management, the C-Suite, or others who can help identify the organization’s CTI needs and potentially, which feeds to procure. Ultimately, stakeholders significantly impact an organization’s overall threat intelligence program.
Finally, and increasingly important today, are third-parties who may be internal, or external, and essential to an organization’s success. Third-parties can be contractors who are part of day-to-day operations, or suppliers who deliver technologies that make modern businesses work — like cloud service providers. CTI can help organizations with multiple aspects of third-party management which may include understanding their exposures, assessing linkages between their brands and supporting third-party capabilities, and addressing IOCs which may impact third-party systems directly connected to internal infrastructure.
Meeting the Needs for All the CTI Users at Each Level of Cyber Threat Intelligence
zveloCTI offers a range of solutions which have been developed to meet the needs for all of the various CTI users across each level of cyber threat intelligence — Strategic, Operational, and Tactical.
- For Strategic CTI Users, zveloCTI supports trend/analysis for individual organizations and industry verticals, as well as overall brand intelligence.
- For Operational CTI Users, zveloCTI supplies IOCs to help provide context around targeted attacks and MCA TTPs which may be used to support threat hunting.
- For Tactical CTI Users, zveloCTI feeds (PhishBlocklist and Malicious Detailed Data Feed) can be used to support incident triage, integrate with existing security systems, and reinforce SOC-type operations.
zveloCTI does the hard work for you. We curate threat data and validate multiple trusted sources so you do not have to, and help reduce costs and the time required to integrate them. As a result, your organization is able to benefit from premium cyber threat intelligence data and services much faster than it would if you were to do all of the work yourself.